南京大学学报(自然科学版) ›› 2021, Vol. 57 ›› Issue (1): 10–20.doi: 10.13232/j.cnki.jnju.2021.01.002
增强深度学习中的差分隐私防御机制
- 1.安徽理工大学计算机科学与工程学院,淮南,232000
2.安徽大学计算机科学与技术学院,合肥,230601
Enhanced differential privacy defense mechanism in deep learning
Fangchao Yu1, Xianjin Fang1( ), Youwen Zhang2, Gaoming Yang1, Li Wang1
), Youwen Zhang2, Gaoming Yang1, Li Wang1
- 1.School of Computer Science and Engineering Anhui University of Science and Technology,Huainan,232000,China
2.School of Computer Science and Technology,Anhui University,Hefei,230601,China
摘要:
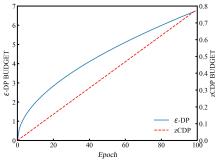
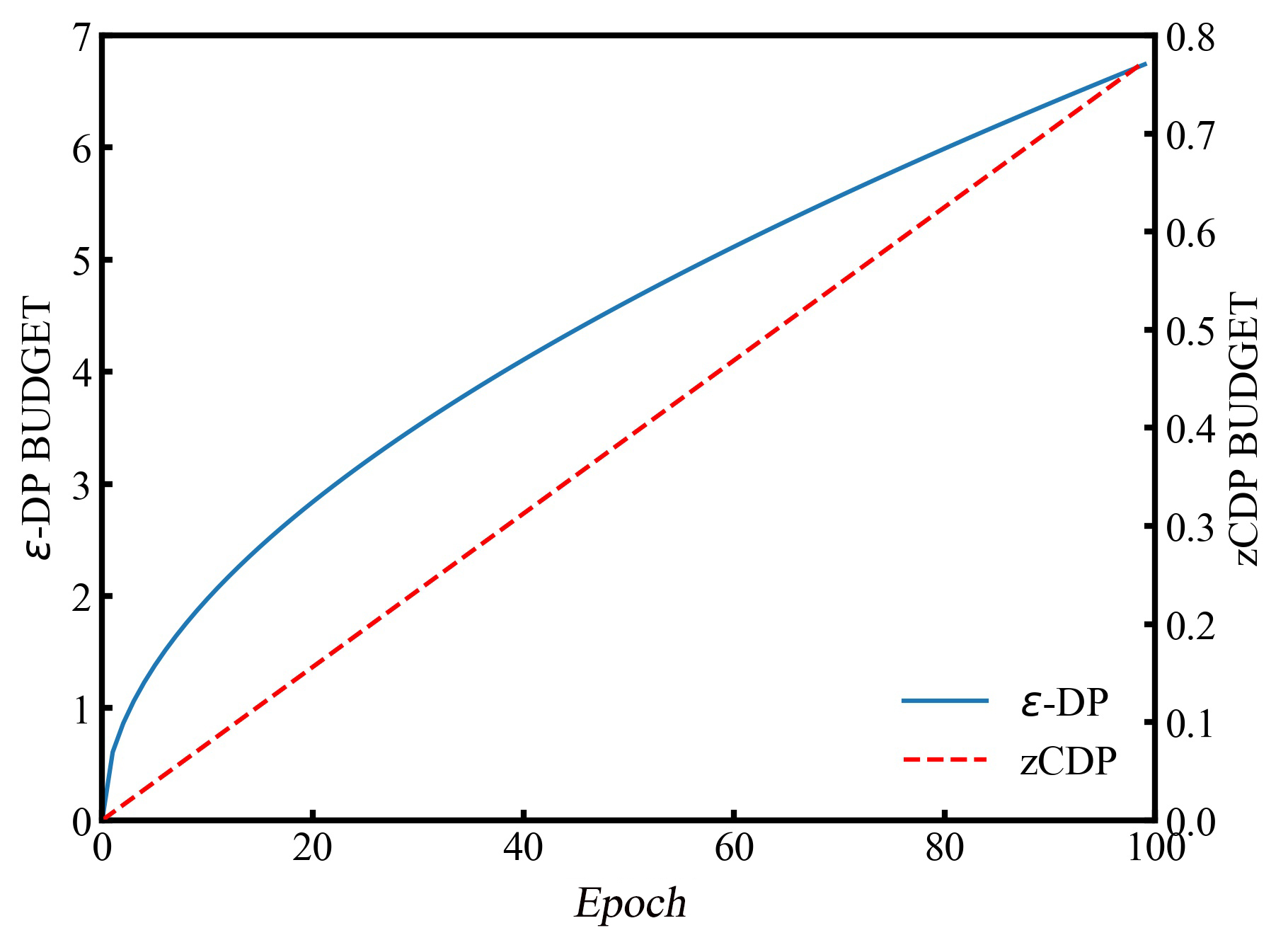
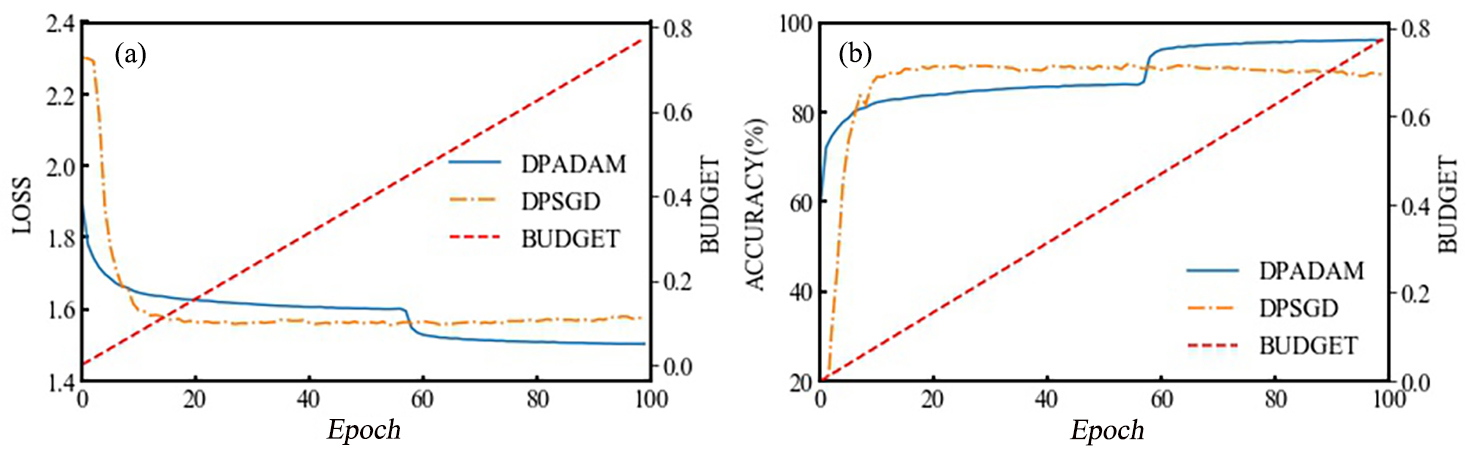
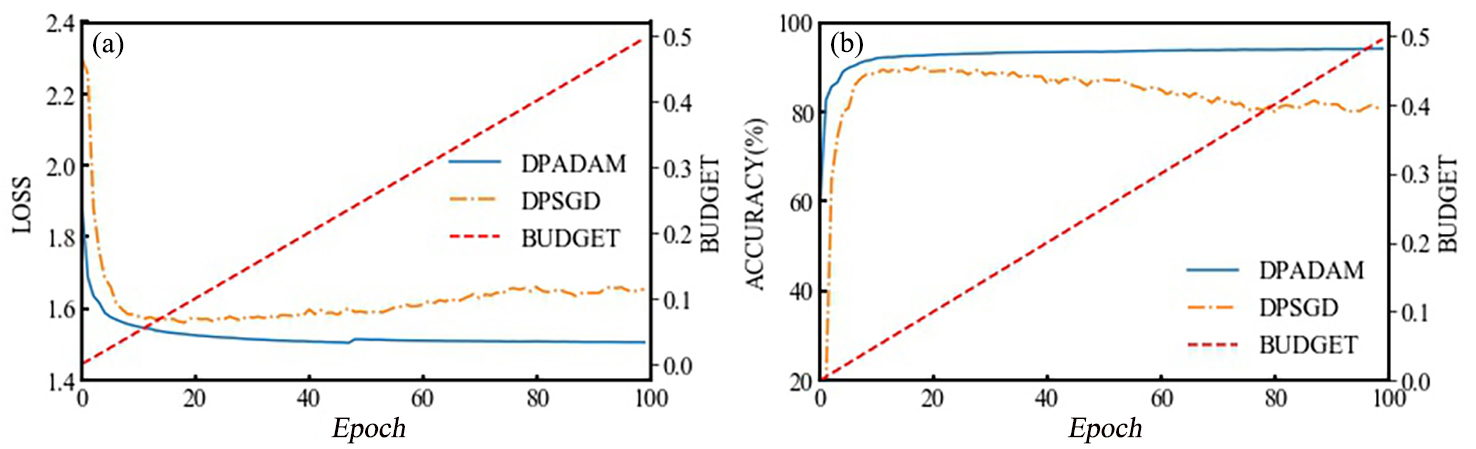
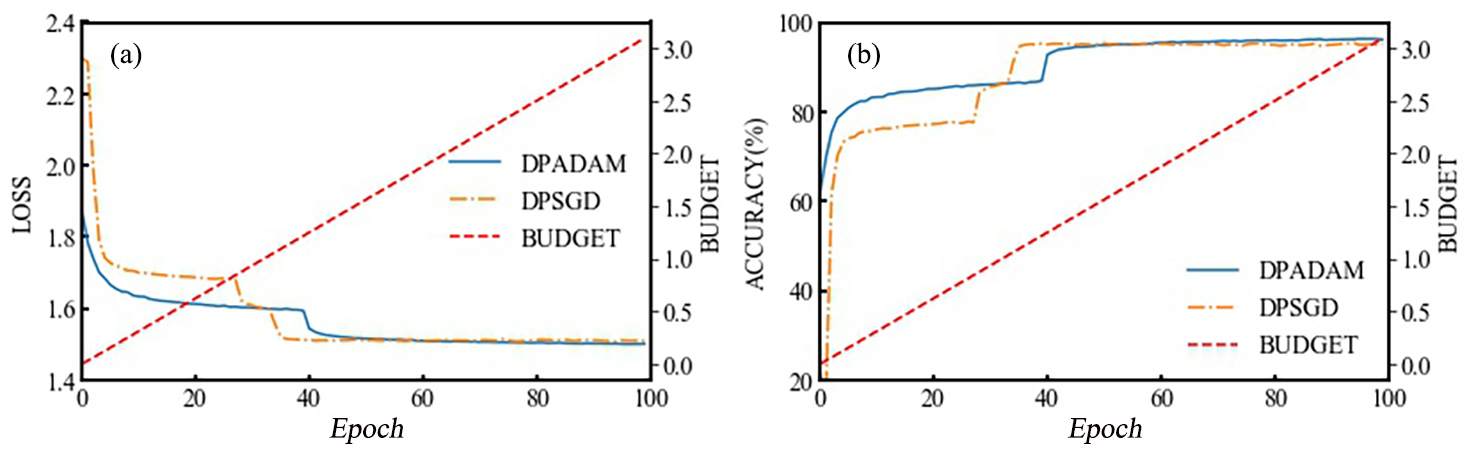
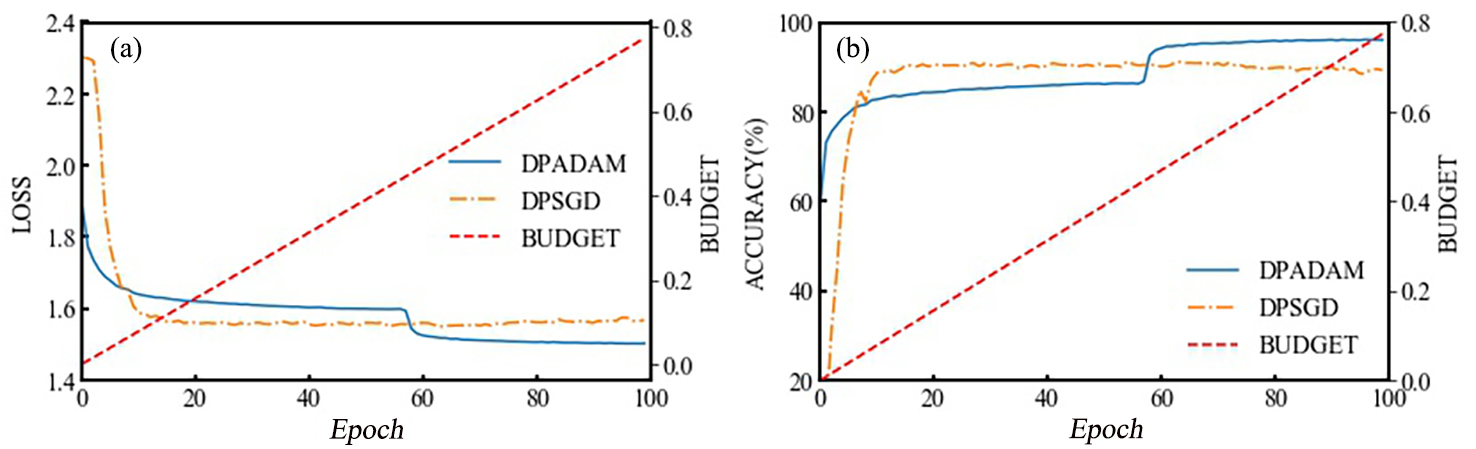
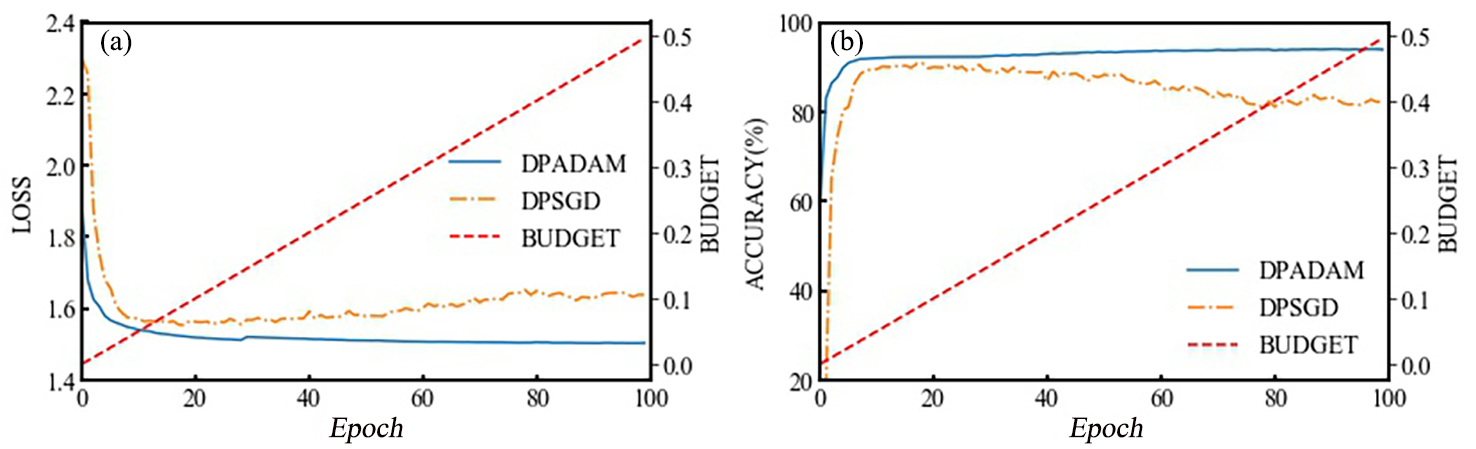
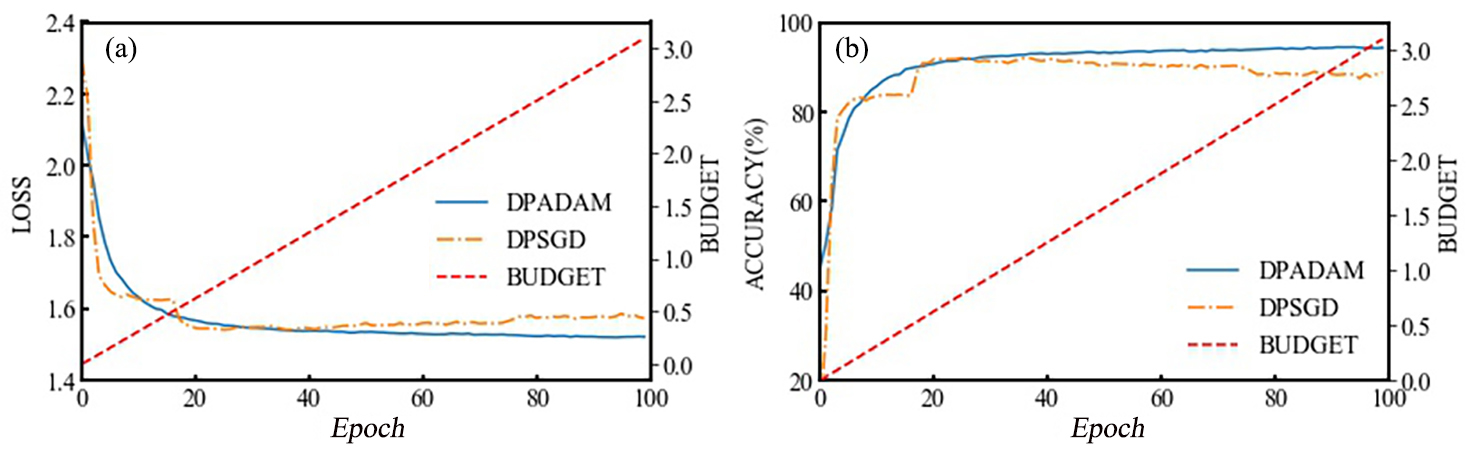
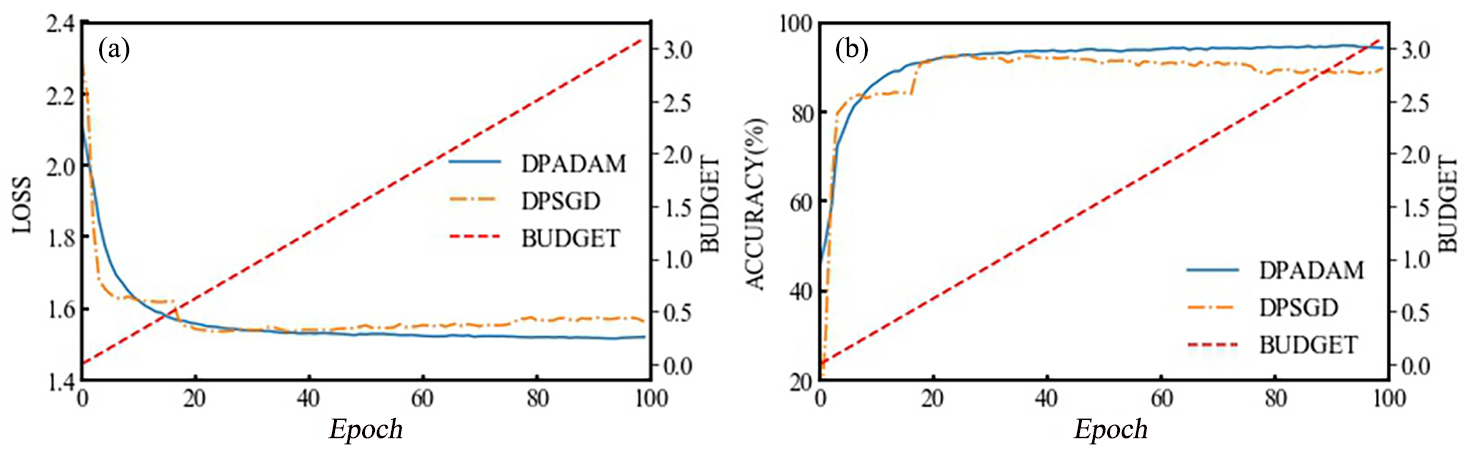
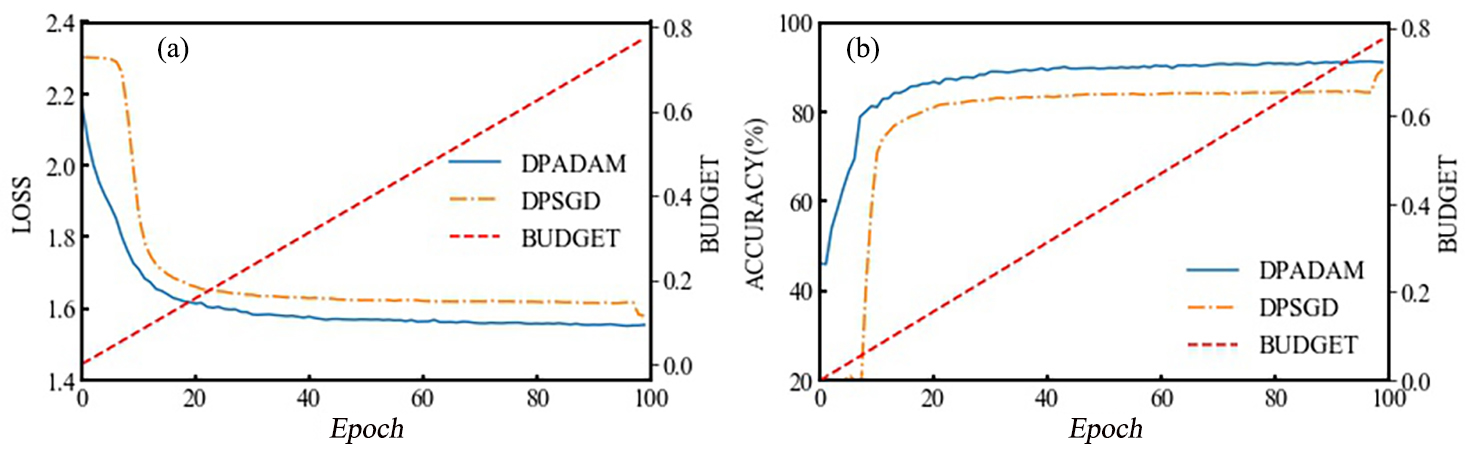
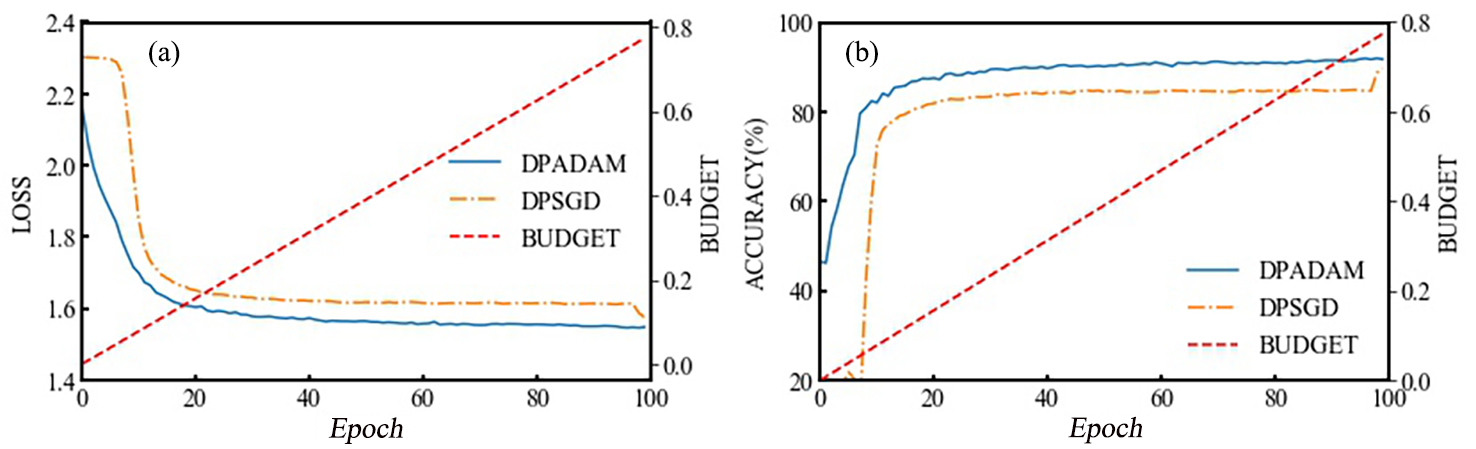
近年来,深度学习在很多领域都得到了广泛的应用,然而基于深度学习的人工智能应用正面临严重的隐私泄露风险,虽然研究人员提出了很多相应的防御机制,但这些方法大都存在以下问题:对攻击者掌握的背景知识有过多的假设、不具有通用性以及高复杂度和高计算代价.尝试从差分隐私的角度出发构造一个通用隐私保护防御算法.目前在深度学习领域,应用最广泛的差分隐私算法是DPSGD(Stochastic Gradient Descent with Differential Privacy),但在应用DPSGD的过程中难以选择合适的参数以达到良好的拟合效果;此外,其隐私损失的度量机制也较为复杂.为解决这些问题,提出DPADAM(Adaptive Moment Estimation with Differential Privacy)算法,同时引入zCDP(Zero?Concentrated Differential Privacy)作为隐私损失的度量机制,使其在应用过程中更加简单灵活.实验证明,DPADAM算法能够有效解决参数依赖问题,在确保隐私性的同时提高模型的拟合效果.
中图分类号:
- TP309.2
| 1 | Voulodimos A,Doulamis N,Doulamis A,et al. Deep learning for computer vision:a brief review. Computational Intelligence and Neuroscience,2018,doi:10.1155/2018/7068349. |
| 2 | Graves A,Mohamed A,Hinton G. Speech recognition with deep recurrent neural networks∥2013 IEEE International Conference on Acoustics,Speech and Signal Processing. Vancouver,Canada:IEEE,2013:6645-6649. |
| 3 | Papernot N,McDaniel P,Sinha A,et al. Sok:security and privacy in machine learning∥2018 IEEE European Symposium on Security and Privacy. London,UK:IEEE,2018:399-414. |
| 4 | Song C Z,Ristenpart T,Shmatikov V. Machine learning models that remember too much∥Proceedings of 2017 ACM SIGSAC Conference on Computer and Communications Security. Dallas,TX,USA:ACM,2017:587-601. |
| 5 | Shokri R,Stronati M,Song C Z,et al. Membership inference attacks against machine learning models∥2017 IEEE Symposium on Security and Privacy. San Jose,CA,USA:IEEE,2017:3-18. |
| 6 | Truex S,Liu L,Gursoy M E,et al. Demystifying membership inference attacks in machine learning as a service. IEEE Transactions on Services Computing,2019,doi:10.1109/TSC.2019.2897554. |
| 7 | Yeom S,Giacomelli I,Fredrikson M,et al. Privacy risk in machine learning:Analyzing the connection to overfitting∥2018 IEEE 31st Computer Security Foundations Symposium. Oxford,UK:IEEE,2018:268-282. |
| 8 | Nasr M,Shokri R,Houmansadr A. Comprehensive privacy analysis of deep learning:passive and active white?box inference attacks against centralized and federated learning∥2019 IEEE Symposium on Security and Privacy. San Francisco,CA,USA:IEEE,2019:739-753. |
| 9 | Fredrikson M,Jha S,Ristenpart T. Model inversion attacks that exploit confidence information and basic countermeasures∥Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security. Denver,CO,USA:ACM,2015:1322-1333. |
| 10 | Gong N Z,Liu B. Attribute inference attacks in online social networks. ACM Transactions on Privacy and Security,2018,doi:10. 1145/3154793. |
| 11 | Narain S,Vo?Huu T D,Block K,et al. Inferring user routes and locations using zero?permission mobile sensors∥2016 IEEE Symposium on Security and Privacy. San Jose,CA,USA:IEEE,2016:397-413. |
| 12 | Tramèr F,Zhang F,Juels A,et al. Stealing machine learning models via prediction apis∥Proceedings of the 25th USENIX Conference on Security Symposium. Berkeley,CA,US:USENIX,2016:601-618. |
| 13 | Wang B H,Gong N Z. Stealing hyperparameters in machine learning∥2018 IEEE European Symposium on Security and Privacy. San Francisco,CA,USA:IEEE,2018:36-52. |
| 14 | Nasr M,Shokri R,Houmansadr A. Machine learning with membership privacy using adversarial regularization∥Proceedings of 2018 ACM SIGSAC Conference on Computer and Communications Security. Toronto,Canada:ACM,2018:634-646. |
| 15 | Jia J Y,Gong N Z. Attriguard:A practical defense against attribute inference attacks via adversarial machine learning∥Proceedings of the 27th USENIX Security Symposium. Baltimore,MD,USA:USENIX,2018:513-529. |
| 16 | Papernot N,Abadi M,ú Erlingsson ,et al. Semi?supervised knowledge transfer for deep learning from private training data. 2016,arXiv:1610.05755. |
| 17 | Zhang T W,He Z C,Lee R B. Privacy?preserving machine learning through data obfuscation. 2018,arXiv:1807.01860. |
| 18 | Dwork C,McSherry F,Nissim K,et al. Calibrating noise to sensitivity in private data analysis∥Theory of Cryptography. New York,NY,USA:Springer,2006:265-284. |
| 19 | Ji Z L,Lipton Z C,Elkan C. Differential privacy and machine learning:a survey and review. 2014,arXiv:1412.7584. |
| 20 | Zhu T Q,Li G,Zhou W L,et al. Differentially private data publishing and analysis:a survey. IEEE Transactions on Knowledge and Data Engineering,2017,29(8):1619-1638. |
| 21 | Abadi M,Chu A,Goodfellow I,et al. Deep learning with differential privacy∥Proceedings of 2016 ACM SIGSAC Conference on Computer and Communications Security. Vienna,Austria:ACM,2016:308-318. |
| 22 | Dwork C,Roth A. The algorithmic foundations of differential privacy. Foundations and Trends? in Theoretical Computer Science,2014,9(3-4):211-407. |
| 23 | Bun M,Steinke T. Concentrated differential privacy:Simplifications,extensions,and lower bounds∥Theory of Cryptography. Beijing,China:Springer,2016:635-658. |
| 24 | Dwork C,Rothblum G N. Concentrated differential privacy. 2016,arXiv:1603.01887. |
| 25 | Kingma D P,Ba J. Adam:A method for stochastic optimization. 2014,arXiv:1412.6980. |
| 26 | Yu L,Liu L,Pu C,et al. Differentially private model publishing for deep learning. 2019,arXiv:1904.02200. |
| [1] | 曾宪华, 陆宇喆, 童世玥, 徐黎明. 结合马尔科夫场和格拉姆矩阵特征的写实类图像风格迁移[J]. 南京大学学报(自然科学版), 2021, 57(1): 1-9. |
| [2] | 张萌, 韩冰, 王哲, 尤富生, 李浩然. 基于深度主动学习的甲状腺癌病理图像分类方法[J]. 南京大学学报(自然科学版), 2021, 57(1): 21-28. |
| [3] | 李一凡, 朱斐, 凌兴宏, 刘全. 具有窗口结构Bi⁃LSTM网络的心电图QRS波检测方法[J]. 南京大学学报(自然科学版), 2021, 57(1): 42-51. |
| [4] | 温玉莲, 林培光. 基于行业背景差异下的金融时间序列预测方法[J]. 南京大学学报(自然科学版), 2021, 57(1): 90-100. |
| [5] | 潘越,王骏,李文飞,张建,王炜. 基于卷积神经网络的蛋白质折叠类型最小特征提取[J]. 南京大学学报(自然科学版), 2020, 56(5): 744-753. |
| [6] | 朱伟,张帅,辛晓燕,李文飞,王骏,张建,王炜. 结合区域检测和注意力机制的胸片自动定位与识别[J]. 南京大学学报(自然科学版), 2020, 56(4): 591-600. |
| [7] | 李康,谢宁,李旭,谭凯. 基于卷积神经网络和几何优化的统计染色体核型分析方法[J]. 南京大学学报(自然科学版), 2020, 56(1): 116-124. |
| [8] | 韩普,刘亦卓,李晓艳. 基于深度学习和多特征融合的中文电子病历实体识别研究[J]. 南京大学学报(自然科学版), 2019, 55(6): 942-951. |
| [9] | 张家精,夏巽鹏,陈金兰,倪友聪. 基于张量分解和深度学习的混合推荐算法[J]. 南京大学学报(自然科学版), 2019, 55(6): 952-959. |
| [10] | 钟琪,冯亚琴,王蔚. 跨语言语料库的语音情感识别对比研究[J]. 南京大学学报(自然科学版), 2019, 55(5): 765-773. |
| [11] | 王蔚, 胡婷婷, 冯亚琴. 基于深度学习的自然与表演语音情感识别[J]. 南京大学学报(自然科学版), 2019, 55(4): 660-666. |
| [12] | 张鹏,黄毅,阮雅端,陈启美*. 基于稀疏特征的交通流视频检测算法[J]. 南京大学学报(自然科学版), 2015, 51(2): 264-270. |
|
||